How real-time SMS fraud detection works
CheckTxt analyzes suspicious SMS messages across multiple fraud signals simultaneously — giving banks, enterprises, and MSSPs visibility into customer-targeted attacks beyond the security stack.
See exactly how the detection works.
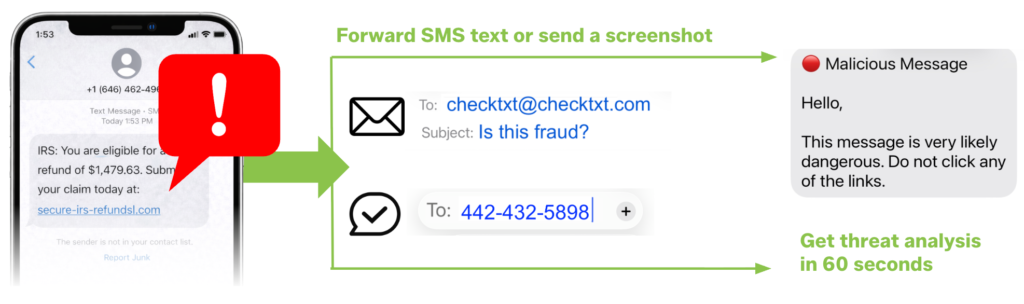
Forward a suspicious message right now!
The same experience your customers, employees, or end users get when they verify a suspicious message.
- Forward a text or send a screenshot → 442-432-5898
- Forward an email or send a screenshot → [email protected]
Verdict returned in under 60 seconds.
How does SMS fraud detection work?
Four steps, under 60 seconds.
CheckTxt analyzes suspicious text messages as soon as they are received.
Before a link is clicked, a payment is made, or personal information is shared.
No app.
No login. No installation.
Works on any device, any carrier.
For individuals, that means knowing whether to delete the message, report it, or act on it.
For organizations, every verdict contributes to a growing picture of who is being targeted, how campaigns are evolving, and where to intervene next.
Protection where fraud actually happens—outside security systems
“Watch CheckTxt CEO Jack Marshall analyze a real toll violation smishing scam live — from forwarding the message to receiving a verdict in under 60 seconds. No app, no account, no setup required.”
How does CheckTxt detect SMS fraud?
Six specialized AI layers working simultaneously.
Patent-Pending CHAI Engine (USPTO 63778,679)
CheckTxt’s patent-pending CHAI engine analyzes suspicious text messages using multiple, specialized detection layers—working together to deliver a clear, accurate verdict in under 60 seconds.
Each layer focuses on a specific fraud signal. Together, they enable real-time SMS fraud and scam detection with zero false positives.
Message content & language analysis
Every SMS scam follows a pattern — urgency, authority, fear, or reward. This layer analyzes the language and structure of each message to identify social-engineering tactics before the recipient acts on them.
Campaign & behavioral pattern detection
Most SMS scams aren’t isolated — they’re coordinated campaigns hitting thousands of customers simultaneously. This layer identifies repeatable patterns across messages, detecting coordinated attacks and AI-generated variants early, before a campaign scales across your customer base.
URL & domain risk assessment
Malicious links are the engine of most SMS scams — designed to steal credentials, install malware, or redirect victims to fake sites. This layer evaluates every embedded link for malicious domains, suspicious redirects, and known fraud infrastructure before a single user clicks.
Sender behavior & anomaly detection
Fraudsters can’t fully hide how they operate. This layer analyzes sender characteristics — number patterns, message timing, volume anomalies, and known bad actor signals — to identify suspicious origin before the message content is even evaluated.
Continuous AI model training
SMS fraud evolves fast — attackers use AI to generate new variants, rotate infrastructure, and adapt messaging in real time. This layer continuously trains on new scam patterns and emerging attack techniques, so detection stays ahead of threats without manual updates or configuration changes.
Impersonation & brand signal detection
Attackers succeed by making messages look like they come from trusted brands — banks, delivery companies, government agencies. This layer analyzes brand impersonation signals, spoofed sender IDs, and message formatting to identify fraudulent messages mimicking organizations your customers trust.
“The CHAI engine was purpose-built for a problem traditional security tools were never designed to solve — fraud that reaches customers directly through SMS, outside enterprise systems, before any transaction occurs. That’s why our SMS fraud protection for banks and SMS fraud protection for enterprises are built on this detection architecture — because stopping fraud at the message level requires a fundamentally different approach than protecting networks and endpoints.”
Privacy-First Architecture
What data does CheckTxt collect and store?
CheckTxt analyzes threats — not people. Here’s exactly what happens with your data:
What we don’t collect:
- No personal information beyond the submitted message content
- No contact lists or address book access
- No location data or device tracking
- No behavioral profiling or usage analytics
- No account creation or password storage
What we do analyze:
- Message content for threat indicators only
- Sender information for pattern recognition
- Embedded links for malicious destination detection
- Metadata patterns for attack vector identification
Message content is deleted immediately after analysis. All communications are encrypted in transit. Your data is never sold. See our Privacy Policy for full details.
Enterprise-grade Azure infrastructure
CheckTxt runs on secure Microsoft Azure infrastructure with privacy-first controls — ensuring fast, reliable analysis at scale. Message content is never stored, aligning with GDPR, CCPA, and enterprise compliance requirements.
Why Existing Security Controls Miss SMS Fraud
- No MDM required - Instant deployment without complex setup
- Personal device friendly - Protect BYOD without privacy invasion
- SMS-specific expertise - Purpose-built for text message threats

- Checktxt’s compound AI engine - demonstrates exceptional accuracy and consistently delivers high-quality results.
- Enterprise management - Centralized control and reporting
- Professional threat intelligence - Real-time analysis, not just blocking

- Direct protection - Actionable results, not just intelligence
- Immediate response - 60-second analysis vs. hours or days
- Proactive takedowns - We eliminate threats, not just report them

It's easy for customers and employees to use.
Try it now!
Frequently Asked Questions
How does CheckTxt deliver a verdict in under 60 seconds?
CheckTxt’s patent-pending CHAI engine analyzes suspicious messages across six specialized detection layers simultaneously — not sequentially. While a traditional rule-based system checks one signal at a time, CheckTxt evaluates message content, sender behavior, embedded links, brand impersonation signals, urgency patterns, and campaign indicators all at once, in under 300ms. The result is a plain-language verdict — scam or legitimate — returned to the user in under 60 seconds, before any damage can occur.
How does CheckTxt deploy to customers without apps or onboarding?
CheckTxt is built on a B2B2C model — banks, enterprises, and MSSPs deploy it directly to their customers and employees without requiring any app downloads, account creation, or enrollment. Customers simply forward a suspicious text to a dedicated number or email a screenshot, and the analysis happens automatically.
Because CheckTxt operates outside the enterprise stack — directly in the customer communication layer — there are no IT integration requirements, no device management dependencies, and no changes to how people communicate. Protection reaches the people attackers target instantly, at any scale.
What is smishing and how does it work?
Smishing is a form of phishing delivered through SMS text messages. Attackers send fraudulent texts impersonating trusted organizations — banks, delivery companies, government agencies, or well-known brands — to trick recipients into clicking malicious links, sharing personal information, or making payments. Unlike email phishing, smishing reaches people on their personal devices where they are more likely to trust and act on messages quickly. Text messages have a 98% open rate and are typically read within minutes of receipt, making SMS one of the most effective channels for social engineering attacks.
As AI-generated messaging and rich communication formats like RCS make smishing more convincing and harder to detect, organizations need real-time protection when a message is received — not after damage has occurred. See a real-world example of a smishing scam targeting consumers right now.
What is the difference between smishing and phishing
Phishing is the broader term for fraudulent messages designed to trick recipients into revealing personal information, clicking malicious links, or making payments. Smishing is phishing delivered specifically through SMS text messages. While email phishing has been a known threat for decades and most organizations have email security controls in place, smishing exploits a channel that most enterprise security stacks don’t monitor — the personal devices and text messages of customers and employees. This makes smishing significantly harder to detect and intercept.
Attackers have shifted toward SMS precisely because it falls outside traditional security visibility, reaches people in moments of trust, and achieves open rates that email can’t match. See how SMS fraud detection for banks addresses smishing at the customer communication layer.
Why can't traditional security tools detect SMS fraud?
Traditional security tools — EDR, SIEM, email security, and endpoint protection — are designed to protect internal systems, networks, and devices. SMS fraud bypasses all of them entirely. Attackers deliberately target customers through text messages because they fall outside enterprise visibility, reaching people on personal devices where no corporate security control has jurisdiction. By the time a fraudulent transaction surfaces in an internal system, the damage has already occurred. Closing this gap requires a different approach — one that operates at the customer communication layer, analyzing suspicious messages as they are received rather than detecting consequences after the fact. See why SMS threat detection for enterprises is the fastest-growing blind spot in enterprise security.
Does CheckTxt detect political donation fraud?
Yes — CheckTxt is the only SMS fraud detection platform with a specialized political scam database, protecting donors from fraudulent requests impersonating candidates, PACs, and political organizations. Detection is nonpartisan, covering all political affiliations, with surge capacity built for election cycles. CheckTxt also coordinates with the FEC, Open Secrets, and ProPublica to stay current on emerging threats. Learn more about political donation smishing scams or see a real-world example of a smishing scam targeting consumers today.
What channels does CheckTxt support?
CheckTxt works across every channel attackers use to reach your customers and employees. Forward suspicious messages from SMS, email, WhatsApp, Signal, or Discord and get the same instant, accurate verdict in under 60 seconds. See how SMS fraud detection works for the full forwarding instructions. For organizations protecting employees across personal devices, see SMS fraud protection for enterprises.
