Bank impersonation attacks have become one of the fastest-growing forms of SMS fraud targeting financial institutions. Attackers send text messages that convincingly mimic official bank communications — account alerts, security warnings, fraud notices — to trick customers into handing over credentials or authorizing payments.
What makes these attacks so damaging is not just their scale. It’s their timing. By the time a bank’s internal systems detect unusual account activity, the customer has already received the message, trusted it, and acted on it.
This post explains how bank impersonation attacks work, why they routinely bypass existing security controls, and what banks can do to deliver SMS fraud protection for banks earlier in the fraud chain.
Why Bank Impersonation Attacks Have Made SMS the Primary Fraud Channel
Attackers are rational. They target where defenses are weakest and victims are most likely to respond. Currently, SMS is the main avenue for financial fraud.
The extent of the problem is undeniable. GASA research indicates that $64.8 billion was stolen from Americans in just one year, with the average victim losing over $1,000. Impersonation scams — where attackers pretend to be trusted institutions like banks — rank among the top five scam types reported. Additionally, 46% of American adults now believe banks should always reimburse scam victims, regardless of the circumstances, which increases the reputational and financial risks for banks, whether or not they were directly responsible.
The attacks are becoming harder to detect. AI-generated content and Rich Communication Services (RCS) now enable attackers to launch highly realistic bank impersonation campaigns at scale — messages that convincingly mimic a bank’s tone, branding, and format in ways that were previously impossible to automate. As Dark Reading reports, 41% of phishing incidents now involve multiple channels, including SMS, and the three fastest-growing human attack methods — smishing, vishing, and quishing — are all mobile-focused.
But the most important factor isn’t the technology. It’s the location.
Bank impersonation attacks occur entirely outside the enterprise perimeter. No endpoint protection detects them. No email gateway inspects them. No SIEM logs capture them. The customer is alone with the message at the exact moment they must decide whether to trust it — and the entire attack relies on that isolation.
Why Bank Impersonation Attacks Bypass Existing Security Controls
Bank impersonation attacks are engineered to succeed precisely because they operate outside the boundaries of traditional security infrastructure. Most bank security controls were built to protect internal systems and employee devices — not customers receiving messages on their personal phones.
The result is a structural blind spot that attackers deliberately exploit:
Transaction monitoring flags suspicious account activity after a customer has already acted on a fraudulent message. By the time an alert fires, the damage is done.
MDM and mobile security platforms are designed for corporate-managed devices. They have no reach into the personal phones your customers use every day.
Email security gateways are purpose-built for email. They cannot inspect, filter, or analyze SMS content in any form.
Consumer spam filters operate at the individual device level. They provide no centralized visibility, no campaign-level pattern recognition, and no way for banks to detect that a coordinated impersonation attack is underway across their customer base.
Awareness training cannot scale fast enough. AI-generated impersonation messages now adapt in real time, producing highly personalized variants that outpace any static training program.
None of these gaps represent a failure of execution. They represent a failure of coverage. Bank impersonation attacks don’t target systems — they target people. And most security stacks were never designed to follow fraud that far.
What Effective SMS Fraud Detection Requires
Closing this gap requires a fundamentally different approach — one designed to operate in the customer communication layer, not inside the enterprise perimeter. Effective SMS fraud detection for banks must:
- Analyze suspicious messages at the moment a customer receives them — before any action is taken
- Detect impersonation signals, malicious links, urgency patterns, and sender anomalies in real time
- Require no app downloads, logins, or enrollment from customers — adoption barriers defeat the purpose
- Correlate submissions across the customer base to surface coordinated campaigns, not just individual incidents
- Provide centralized visibility to fraud and security teams — not just verdicts to individual customers
- Integrate alongside existing fraud controls without replacing or disrupting current workflows
The intervention point that matters most is before the click, the credential entry, or the wire transfer. Once a customer acts, the fraud chain is already in motion.
From Isolated Reports to Campaign-Level Intelligence
One of the biggest limitations of current fraud reporting is fragmentation. When customers report suspicious texts one by one — to the bank’s call center, to the FTC, or not at all — the institution sees isolated incidents instead of recognizing the coordinated attack behind them.
This matters because SMS impersonation campaigns rarely target just one customer. Attackers run high-volume campaigns across a bank’s entire customer base at the same time, tweaking messaging as they go. Without shared visibility into these efforts, fraud teams can’t see the campaign developing; they only see the losses after they happen.
This aligns with what the larger industry recognizes. At the UN Global Fraud Summit in March 2026, 11 major industry groups, including Google, Microsoft, and Meta, signed the Industry Accord Against Online Scams and Fraud, explicitly pledging to share threat intelligence across organizations to detect emerging fraud patterns more quickly. The accord shows what fraud teams already understand: no single organization can see the full scope of a coordinated campaign without sharing intelligence.
When suspicious messages submitted by customers are correlated at the platform level, campaigns become visible while they are still forming — giving banks a window to issue proactive advisories before losses accumulate, not after.
The Regulatory and Liability Dimension
Consumer expectations around bank fraud accountability are high and rising. GASA research found that 46% of American adults believe banks should always be responsible for reimbursing scam victims — placing banks at the same level of accountability as credit card companies in the public’s view. Banks are also rated #1 among all institutions for actually preventing and resolving scams — meaning the gap between expectation and performance is highly visible to regulators and customers alike.
Regulators are paying attention. The CFPB and OCC are increasingly expecting financial institutions to take proactive measures to protect customers from digital impersonation fraud — not just reimburse them after harm occurs. Implementing a detection control at the customer communication layer provides a documented, active intervention that shows proactive consumer protection to examiners.
It also lessens the downstream effects that trigger regulatory scrutiny initially: fraud complaints, reimbursement volumes, and customer harm incidents identified during examinations.
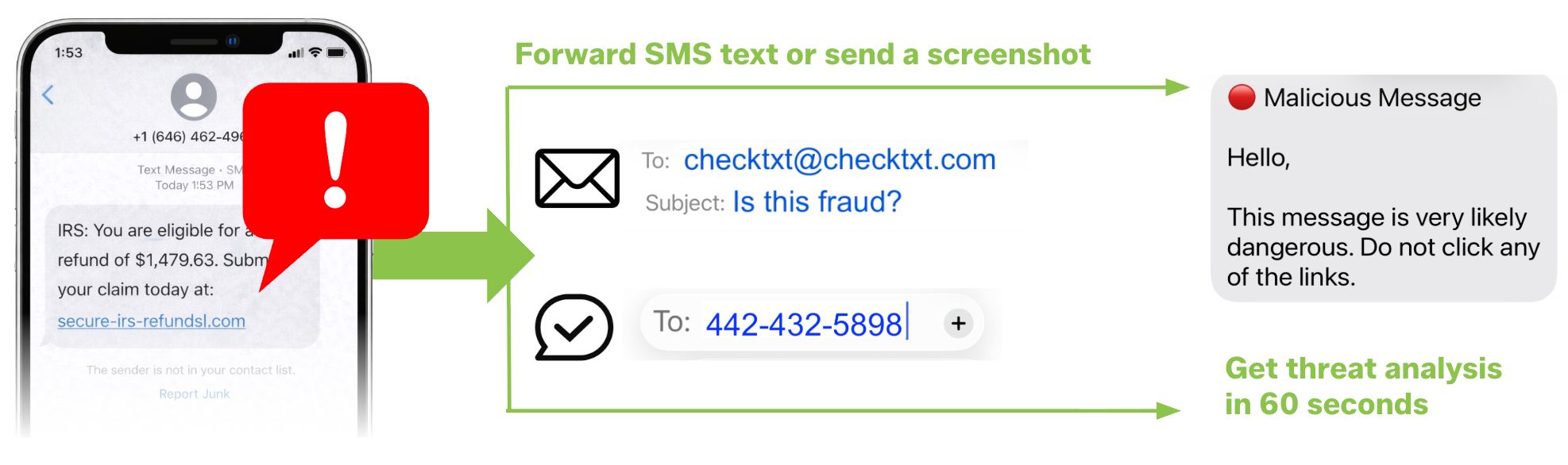
Report Suspicious Messages to CheckTxt
The best way to understand what CheckTxt does is to try it. If you receive a suspicious text message, or if your customers are currently being targeted by an impersonation campaign.
- Forward a text or send a screenshot → 442-432-5898
- Forward an email or send a screenshot → [email protected]
Forward a message to CheckTxt and receive a fraud verdict in under 60 seconds.
How Banks Can Intervene Earlier in Bank Impersonation Attacks
The coverage gap above cannot be closed by adding another internal security control. The attack happens outside the enterprise — so the protection needs to operate there too.
CheckTxt operates directly inside the customer communication layer, complementing existing fraud, risk, and compliance controls without replacing or disrupting them.
Here’s how it works:
- A customer receives a suspicious text claiming to be from their bank
- They forward the SMS or send a screenshot to CheckTxt — no app, no login, no onboarding
- CheckTxt analyzes the message in real time for impersonation signals, brand spoofing, malicious URLs, and sender anomalies
- The customer receives a plain-language verdict in under 60 seconds
- Every submission is correlated across the bank’s customer base, giving fraud teams visibility into active campaigns — not just isolated reports
This is the B2B2C model that bank impersonation attacks demand: protection that reaches customers at scale, without app management or onboarding overhead.
Learn more about how SMS fraud detection works or see how CheckTxt delivers SMS fraud protection for banks.
Frequently Asked Questions (FAQs)
Does CheckTxt replace our existing fraud tools?
No. CheckTxt operates outside the traditional security stack, in the customer communication layer, where existing fraud and security controls have no visibility. CheckTxt complements your current fraud, risk, and SIEM tools by catching threats when a customer receives a suspicious message, before any transaction occurs that your existing systems would flag. No workflow changes, no integration requirements, no displacement of current controls.
How do bank customers actually use CheckTxt?
Customers simply forward a suspicious text or send a screenshot to CheckTxt — no app download, no account, no onboarding required. CheckTxt analyzes the message in real time for impersonation signals, malicious links, urgency patterns, and sender anomalies, then returns a plain-language verdict in under 60 seconds. CheckTxt works on any device and any carrier, making it practical to extend protection to your entire customer base without support overhead.
What does a bank actually see and get access to?
CheckTxt provides fraud and security teams with real-time visibility into SMS-based attacks targeting their customers, not just isolated incident reports. As customers forward suspicious messages, CheckTxt correlates submissions across the customer base to detect coordinated impersonation campaigns as they develop. This enables your team to spot emerging attack patterns early enough to issue proactive customer advisories, rather than discovering a campaign only after losses have accumulated.
How does CheckTxt support regulatory and compliance requirements?
Regulators increasingly expect financial institutions to demonstrate proactive consumer protection — not just reactive reimbursement. CheckTxt establishes a documented, active control at the customer communication layer, showing examiners that your institution intercepts impersonation fraud before harming customers. CheckTxt also decreases the number of fraud complaints and customer harm incidents, which typically draw regulatory scrutiny.
