About CheckTxt
Built from the ground-up to solve the fraud problem the rest of the industry left behind.
CheckTxt was built by a team that had spent over 60 years inside the security industry — across some of the most influential companies the space has ever produced. Fortify, acquired by HP. AlienVault, acquired by AT&T. Phantom, acquired by Splunk. WhiteHat Security, acquired by Synopsys. Appthority, acquired by Symantec. Valimail, acquired by DigiCert. Synopsys/Black Duck. Contrast Security. Bolster.
Nine acquisitions between us.
Categories created.
Enterprises protected.
And yet, everywhere we looked, the same blind spot existed. The people outside the firewall — employees on personal devices, customers on personal phones — were completely unprotected. No tool was built for them. No budget owned them. The channels attackers used to reach them — SMS, email, messaging apps — fell outside every security stack we’d ever worked on.
We designed CheckTxt from the ground up to be different, to protect people, not just infrastructure.

Jack Marshall
Co-Founder & CEO
Jack is a serial entrepreneur with a track record of building and scaling technology companies from startup to acquisition. Jack founded Photoloft in 1998, taking the company public before its acquisition by Canon. He went on to hold senior leadership roles across leading cybersecurity companies, including Fortify, AlienVault, Prevoty, and Contrast Security, and most recently served as CEO of Bolster, an AI-powered brand protection platform combating digital fraud at scale.
Jack earned a BSEE with a Computer Engineering minor from Michigan State University. Graduate coursework in Electrical Engineering, Santa Clara University.

Rick Bowen
CTO
Rick is a proven engineering leader with deep experience building and scaling enterprise security platforms. Rich spent over a decade at HP and ArcSight, serving as Senior Director of R&D at ArcSight, a pioneer in SIEM security. He later served as VP of Engineering at Phantom, helping scale the SOAR platform prior to its acquisition by Splunk, and went on to lead strategy and operations at Synopsys through the successful spin-out of Black Duck.
Rick earned a BS in Electrical and Computer Engineering and an MEng in Engineering Management at Cornell University.
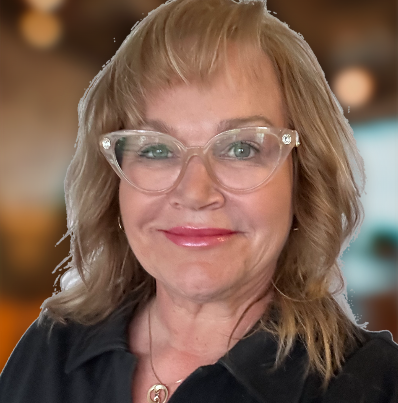
Christine Carrig
VP of Marketing
Christine Carrig brings 20 years of experience building revenue engines for cybersecurity companies. She has led growth initiatives at Contrast Security, CyCognito, Valimail, WhiteHat Security, and Appthority — building demand-generation systems from the ground up and scaling pipelines from early traction to multi-million-dollar revenue impact.
At CheckTxt, Christine serves as the founding marketer, defining product narrative and messaging architecture, and building demand-generation efforts.
Christine holds a BA in Management, with honors, from Saint Mary’s College of California.

Myles Albaladejo
Head of Development
Myles is a mathematically trained technologist and cybersecurity-focused software developer with experience building secure, data-driven systems. Myles began his career at Symantec and later joined Gen Digital, gaining hands-on experience at the intersection of security, infrastructure, and application development. At CheckTxt, he built the core technology powering the platform — bringing analytical rigor and engineering discipline to tools that help people identify and avoid digital threats.
Myles earned a BS from the University of California, San Diego.
Our Trusted Advisors

Pete Thompson
CMO Consulting Group,
Amazon, eBay, Microsoft
CMO & Chief Product Officer

Joe Rodgers
Bank OZK
IT Security

Chris Deleon
Paradigm
Director of Cyber Defense & Security Engineering

Christopher Martinkus
UMB
VP of Threat Intelligence

Boubacar Camara
Mixx Senegal
Head of Risk & Compliance

Eric Budke
Neuberger Berman Group, LLC
Head of Security Engineering
Jack will explain how CheckTxt works. It won't take long.
Two minutes with our CEO — part product demo, part proof that stopping fraud doesn’t have to be complicated.
The Mind Behind CheckTxt
Jack Marshall has spent his career building technology companies that solve problems others overlook.
Starting in the late 1990s, Jack founded Photoloft — one of the first online photo-sharing platforms — taking the company public before its acquisition by Canon. Over the next two decades he held leadership roles across some of the most influential cybersecurity companies in the industry, from Fortify and AlienVault to Contrast Security and Bolster — companies that collectively shaped how enterprises think about security.
But it was a text message to a family member that sharpened everything into focus.
Not a sophisticated attack. Not a nation-state threat. Just a convincing scam targeting someone he loved — someone with no firewall, no security team, and no way to know whether to trust what was in front of them. It was the same blind spot he’d seen inside every enterprise he’d ever worked in, playing out in real life, on a personal phone, in a moment that mattered.
That’s what CheckTxt is built to prevent.
“We don’t just protect systems. We protect people.”

