Smishing Attacks Bypass Everything You've Built to Stop Them
SMS attacks arrive on personal devices, through personal numbers, on a channel your security stack has never monitored. CheckTxt closes the gap.
The Smishing Attack
Social engineering via text — at scale
Attackers send SMS messages impersonating your brand, your IT department, your executives, your vendors, and your bank. No malware. No attachments. Just a convincing message that moves people to act — hand over credentials, approve a transfer, click a link, make a payment.
The targets aren’t just inside your organization. Customers receive fake messages impersonating your brand. Vendors get texts redirecting payments. Executives are targeted at home, on personal devices, outside business hours.
The Security Gap
The blind spot in your enterprise SMS security
Your firewall doesn’t see it. Your email filter doesn’t touch it. Your EDR has nothing to flag. SMS arrives on personal devices, customer phones, and partner numbers — completely outside your security stack.
By the time someone hands over a verification code, wires funds to the wrong account, or falls for a messaging fraud attack, your SIEM still hasn’t logged a single event. The attack is over before your tools know it started.
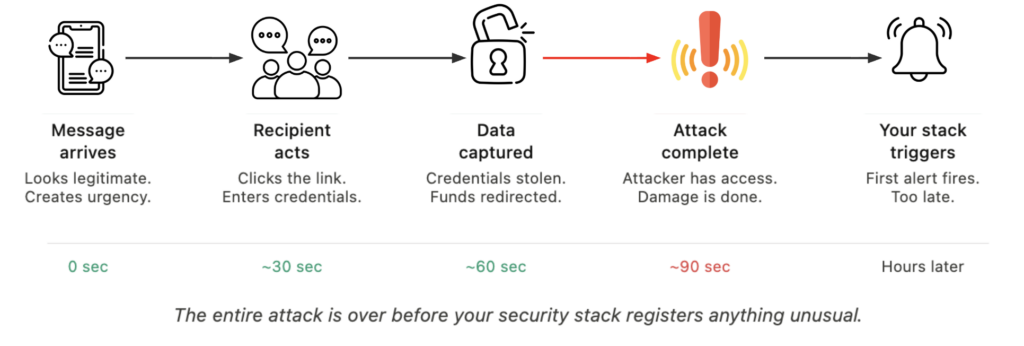
What Happens When Smishing Lands
Smishing attacks don’t announce themselves.
By the time the damage is visible, the attack is already complete.
Credential theft happens in seconds. A convincing message. A login portal that looks right. Credentials handed over — no malware, no endpoint flagged, nothing in your SIEM. The breach happened before your security stack logged a single event.
Financial fraud follows the same pattern. Fake payment instructions, a vendor changing bank details, an executive requesting an urgent wire. By the time it’s questioned, the funds are gone.
Brand damage outlasts the attack. When attackers impersonate your brand to reach your customers, the association sticks. What they remember is that something went wrong — and your name was on it.
Regulators expect more than an explanation. Proactive steps to protect customers from digital fraud are increasingly the standard — not explanations of why existing tools weren’t built for this channel.
Each of these outcomes occurs before your security stack registers anything unusual.
How CheckTxt Stops Smishing Attacks Before Damage Occurs
CheckTxt operates where your security tack stops — at the message itself. Before anyone clicks, transfers, or responds.
Detection at the moment of receipt
Smishing works because people act before they think. CheckTxt intercepts that moment. Suspicious messages are forwarded for analysis and return a verdict in under 60 seconds — before credentials are entered, before funds move, before a link is clicked.
No apps, no onboarding, no friction
Tools that require installation or enrollment don't get used when it matters. CheckTxt works on any device, through any number, with no app download and no account required. Forward a message. Get a verdict.
Campaign-level visibility
Individual smishing attacks are rarely isolated. Submitted messages are correlated across your organization to identify coordinated campaigns as they form, not after multiple people have been hit. Your security team gains visibility into who is being targeted, at what scale, and by what method.
Works alongside your existing stack
CheckTxt doesn't replace your existing controls. It fills the one gap they all share — the channel none of them monitor.
No workflow changes, no integration burden. SMS fraud protection for enterprises →
Protect yourself by protecting your customers
Smishing is the gap in every security stack.
CheckTxt closes it.
Live Admin Dashboard
Real-Time Visibility Into Every Threat Targeting Your Customers
Your fraud team shouldn’t be the last to know.
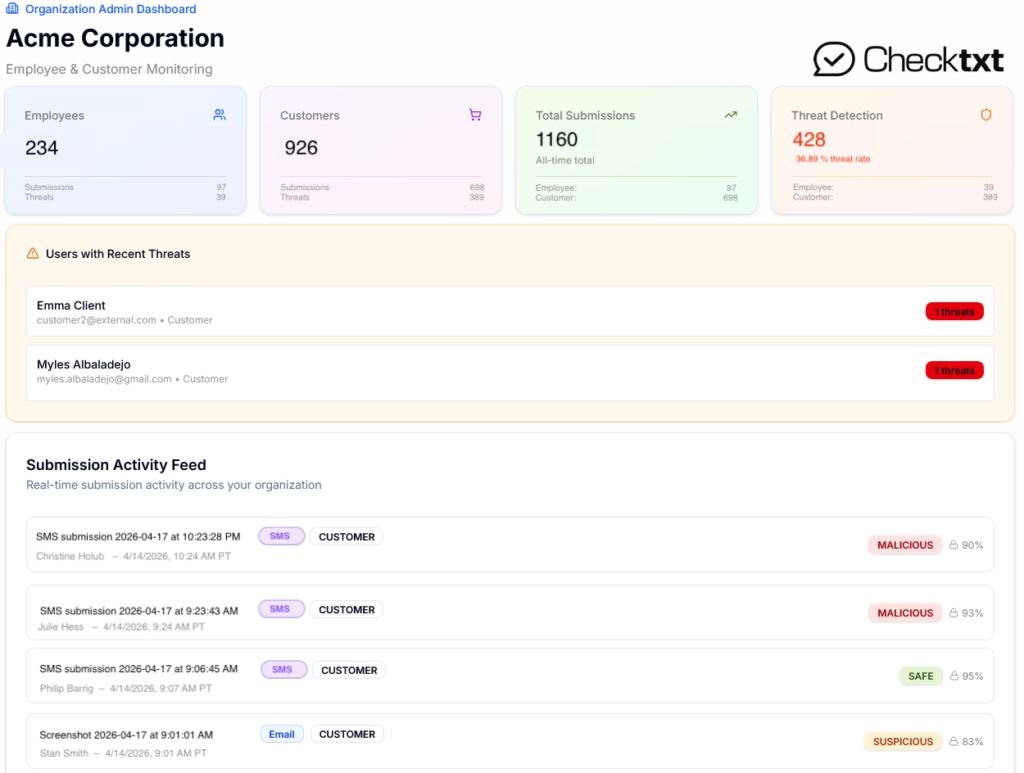
The CheckTxt Admin Dashboard gives bank fraud and security teams a live view into every suspicious message submitted across their customer base — not as an end-of-day report, but as it happens.
926 customers monitored. 389 threats detected. A 36.89% threat rate — visible in real time, not discovered after losses occur.
The Submission Activity Feed returns a Malicious, Suspicious, or Safe verdict with a confidence score in under 60 seconds, so your team sees the threat before the customer acts on it.
No aggregated reports.
No end-of-month summaries.
Just a live intelligence layer operating exactly where your existing security stack has no visibility: inside your customers’ messages.
Frequently Asked Questions
Why can't my existing security stack detect smishing?
Your firewall, email filter, EDR, and SIEM were built to monitor network traffic and corporate devices. Smishing arrives on personal devices through personal phone numbers — completely outside the perimeter those tools monitor. There is no packet to inspect, no email header to flag, no endpoint to alert. The attack operates on a channel your stack has never had visibility into.
How do smishing attacks lead to account takeover?
SMS has a 98% open rate compared to roughly 20% for email.
Messages arrive on personal devices where people are less guarded, there’s no spam filter, and the small screen makes it harder to scrutinize links and sender details. AI-generated messages have eliminated the grammatical errors that once helped people spot fakes. The result is an attack that’s faster, more convincing, and far harder to catch.
How does AI make smishing attacks harder to detect?
AI allows attackers to generate grammatically perfect, contextually accurate messages at scale — indistinguishable from legitimate communications. They can replicate your brand’s tone, personalize messages using publicly available data, and launch thousands of variants instantly, adapting in real time to avoid pattern-based detection. Signature-based tools were built for a different era.
How can I tell if a text message is really from my bank?
Attackers send a message impersonating IT, a bank, or a trusted vendor, directing the recipient to a login page that appears legitimate. Credentials entered on that page go directly to the attacker. With valid credentials, they can bypass most enterprise authentication controls, access systems, and move laterally before anyone notices. No malware is involved, which means no endpoint detection triggers.
Can smishing target my customers, not just my staff
Yes — and this is one of the most underappreciated risks. Attackers regularly impersonate brands to target their customers directly via SMS. Your customers receive a convincing message appearing to come from you, act on it, and suffer the financial and reputational harm. Your security stack has no visibility into this at all. See how brand impersonation via SMS works →
