The fraud protection layer your security stack is missing
SMS fraud bypasses every control you have. CheckTxt operates where your stack ends — inside the message, before the click.
SMS fraud doesn’t trigger your firewall.
It doesn’t touch your endpoint.
It doesn’t appear in your SIEM.
It lands directly in your customer’s hand.
The CheckTxt Platform
Five integrated layers. One architecture.
CheckTxt is built to detect, correlate, and disrupt messaging-based fraud at every stage — from the moment a message lands to the moment a threat is shut down.
1.
Patent-pending CHAI Engine
Channel-agnostic, ML-driven behavioral analysis trained on messaging fraud at the signal level.
Analyzes message structure, sender behavior, URL risk, and linguistic patterns simultaneously — identifying the behavioral anatomy of a scam, not just signatures.
2.
Threat Intel & Enforcement Engine
Indicator correlation, intelligence sharing, and direct enforcement action.
Aggregates threat indicators across channels to map coordinated fraud efforts. LLM-powered takedown automation reduces time between detection and disruption.
3.
Conversation Correlation Engine
Correlates multi-step conversations to catch what single-message analysis misses.
Builds a unified interaction graph across channels, regardless of message origin — tracking how trust is built, pressure is applied, and victims are moved toward action.
4.
Threat Intelligence Center
A command center dashboard that provides a view of every submission, every channel, every threat.
Identity-level tracking ties every submission to a named individual, not just an alert. Confidence-scored verdicts — malicious, suspicious, or safe — with probability per decision.
5.
CheckTxt Intercept App
Real-time scam intervention on the user’s device — before the click, before the transfer, before the damage.
Detonates suspicious links in a sandboxed environment before the user touches them. Triggers on the behavioral anatomy of a scam, not just known signatures.
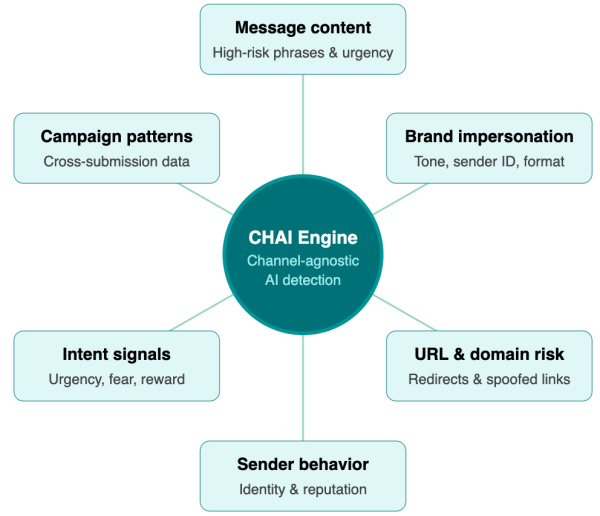
The CHAI Engine
Six specialized AI layers working simultaneously
CheckTxt’s patent-pending CHAI engine analyzes suspicious text messages using multiple, specialized detection layers—working together to deliver a clear, accurate verdict in under 60 seconds.
Each layer focuses on a specific fraud signal. Together, they enable real-time detection of SMS fraud and scams.
Patent-Pending CHAI Engine (USPTO 63778,679)
CheckTxt runs on secure Microsoft Azure infrastructure. Message content is analyzed and immediately deleted — never stored, never sold — in alignment with GDPR, CCPA, and enterprise compliance requirements.
Why existing controls fall short
SMS fraud lives outside every tool you already own
MDM, spam filters, and security training were designed to protect systems — not to detect fraud at the moment a customer reads a text. That's the gap attackers exploit.
|
CheckTxt
Only purpose-built
|
MDM & mobile security
CrowdStrike, Lookout
|
Consumer spam filters
Robokiller, Truecaller
|
Email & phishing tools
Proofpoint, Abnormal
|
|
|---|---|---|---|---|
| Real-time SMS analysis at message receipt | ✓ | – | ~ | – |
| Extends protection to customers (B2B2C) | ✓ | – | – | – |
| No app, login, or enrollment required | ✓ | – | – | – |
| Works on any device and carrier (BYOD) | ✓ | – | ~ | – |
| Centralized campaign-level threat intelligence | ✓ | – | – | ~ |
| AI-driven content and sender fraud detection | ✓ | ~ | ~ | ✓ |
| Verdict returned in under 60 seconds | ✓ | – | – | – |
| Scales to millions of end users with no support burden | ✓ | – | – | – |
|
Fully supported
Partial or limited
Not supported
|
||||
Protection that works where
your customers are.
Your customer receives a verdict before they act.
Your team gains visibility while the attack is still forming.
Frequently Asked Questions
How does CheckTxt deliver a verdict in under 60 seconds?
CheckTxt’s patent-pending CHAI engine analyzes suspicious messages across six specialized detection layers simultaneously — not sequentially. While a traditional rule-based system checks one signal at a time, CheckTxt evaluates message content, sender behavior, embedded links, brand impersonation signals, urgency patterns, and campaign indicators all at once, in under 300ms. The result is a plain-language verdict — scam or legitimate — returned to the user in under 60 seconds, before any damage can occur.
How does CheckTxt deploy to customers without apps or onboarding?
CheckTxt is built on a B2B2C model — banks, enterprises, and MSSPs deploy it directly to their customers and employees without requiring any app downloads, account creation, or enrollment. Customers simply forward a suspicious text to a dedicated number or email a screenshot, and the analysis happens automatically. See how it works for customers and try it yoursefl!
Because CheckTxt operates outside the enterprise stack — directly in the customer communication layer — there are no IT integration requirements, no device management dependencies, and no changes to how people communicate. Protection reaches the people attackers target instantly, at any scale.
What is the difference between smishing and phishing
Phishing is the broader term for fraudulent messages designed to trick recipients into revealing personal information, clicking malicious links, or making payments. Smishing is phishing delivered specifically through SMS text messages. While email phishing has been a known threat for decades and most organizations have email security controls in place, smishing exploits a channel that most enterprise security stacks don’t monitor — the personal devices and text messages of customers and employees. This makes smishing significantly harder to detect and intercept.
Attackers have shifted toward SMS precisely because it falls outside traditional security visibility, reaches people in moments of trust, and achieves open rates that email can’t match. See how SMS fraud detection for banks addresses smishing at the customer communication layer.
Why can't traditional security tools detect SMS fraud?
Traditional security tools — EDR, SIEM, email security, and endpoint protection — are designed to protect internal systems, networks, and devices. SMS fraud bypasses all of them entirely. Attackers deliberately target customers through text messages because they fall outside enterprise visibility, reaching people on personal devices where no corporate security control has jurisdiction. By the time a fraudulent transaction surfaces in an internal system, the damage has already occurred. Closing this gap requires a different approach — one that operates at the customer communication layer, analyzing suspicious messages as they are received rather than detecting consequences after the fact. See why SMS threat detection for enterprises is the fastest-growing blind spot in enterprise security.
