Enterprise security stops at the edge. SMS fraud doesn’t.
SMS fraud doesn’t breach your perimeter protection. It goes around it.
Reduce your exposure beyond the enterprise perimeter
Earlier intervention.
Fewer downstream consequences.
As messaging-based fraud is identified across SMS, email, and voice, each interaction contributes to a shared threat intelligence layer. Patterns, infrastructure, and tactics observed in one channel inform detection across the others, allowing enterprises to see campaigns earlier and respond faster. Instead of isolated alerts, teams gain a unified view of how fraud is evolving across customer-facing communications—turning individual incidents into actionable, enterprise-wide intelligence.
CheckTxt operates beyond your current security stack
Outside the enterprise stack.
Inside customer communications.
CheckTxt operates beyond internal systems, extending enterprise security into customer-facing messaging—where SMS, email, and voice fraud actually occur.
It complements existing security and fraud controls by operating in the path of messages customers trust and act on, without requiring apps, onboarding, or workflow changes.
Built for the Problems Enterprises Actually Have
The gaps in your security stack are where employees and customers get hit. Here’s how CheckTxt closes them.
SMS attacks reach employees and customers where your security stack can't see.
SMS attacks target employees and customers outside your security stack — where none of your existing controls can see them.
By the time you have visibility, the attack is already underway.
By the time your team connects the dots, the campaign has already scaled across your employee and customer base.
Attackers borrow your brand. You absorb the damage.
CheckTxt correlates submissions across your entire customer base, so your fraud team sees active impersonation campaigns while they're still forming — not after losses accumulate.
Built for the Problems Enterprises Actually Have
The gaps in your security stack are where employees and customers get hit, here’s how we close them.
Most enterprises don’t know an attack is underway until after the damage is done.
Real-time, multi-signal threat analysis uses compound AI engines to analyze message content, sender information, and embedded links as messages are received. Pattern recognition identifies sophisticated attack vectors and emerging threats, while continuous learning adapts detection in real time as attacker behavior evolves—allowing fraud to be identified before customer action occurs.
Cross-channel threat intelligence correlation connects signals across messaging channels, enabling early detection of scam campaigns even as attackers shift tactics or infrastructure.
Active threat elimination and disruption target malicious domains, links, and delivery infrastructure to reduce repeat exposure and prevent isolated attacks from becoming systemic risk.
Relationships with hosting and infrastructure providers accelerate takedown responses. Formal UDRP complaints are filed through a Washington, D.C.–based law firm to remove malicious domains at the source.
Real-time dashboards provide visibility into active threats across SMS, email, and voice. Privacy-first data handling ensures message content is never stored, aligning with GDPR, CCPA, and enterprise compliance requirements.
ROI tracking ties fraud reduction to measurable outcomes, and built-in Security Advisory templates enable rapid customer and employee notifications during active campaigns.
Our API-first integrations and enterprise architecture expose verdicts, campaign signals, and threat intelligence via secure APIs and native SIEM connectivity. This enables teams to operationalize messaging fraud intelligence within existing detection, response, and case-management systems.
Built on Azure-based cloud infrastructure, the platform delivers enterprise-grade security, global scalability, and high availability—without device agents, customer enrollment, or changes to endpoint posture.
RBAC enforces least-privilege access across teams and business units. Multi-tenant architecture supports secure deployment across subsidiaries, departments, and partner organizations — so each stakeholder sees exactly what they need to, and nothing they don't.
When customers can't tell a legitimate message from a fraudulent one, your brand absorbs the damage.Branded protection for verified communications reinforces authenticity at the moments it matters most — reducing the impact of impersonation and preserving customer trust.
Live Admin Dashboard
One View. Every Employee. Every Customer. Every Threat.
Most enterprises don’t know an attack is underway until after the damage is done.
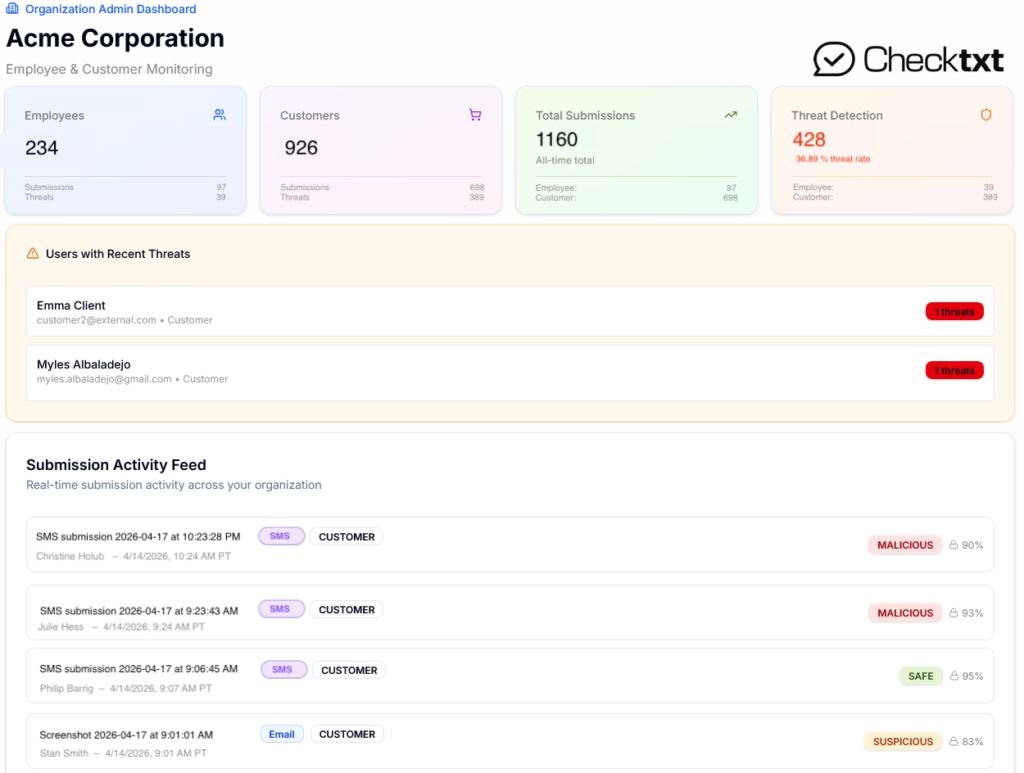
The CheckTxt Admin Dashboard gives security and fraud teams unified visibility across both sides of their exposure — employees and customers — in a single real-time view.
234 employees monitored. 926 customers protected. 428 threats detected at a 36.89% threat rate — all visible as it happens, not surfaced in a Monday morning report. The Submission Activity Feed returns a Malicious, Suspicious, or Safe verdict with a confidence score in under 60 seconds, across SMS and email.
No aggregated reports.
No blind spots between your internal stack and your customer base.
Just a live intelligence layer that operates exactly where enterprise security controls stop — and messaging fraud begins.
